Authentication vs Authorization
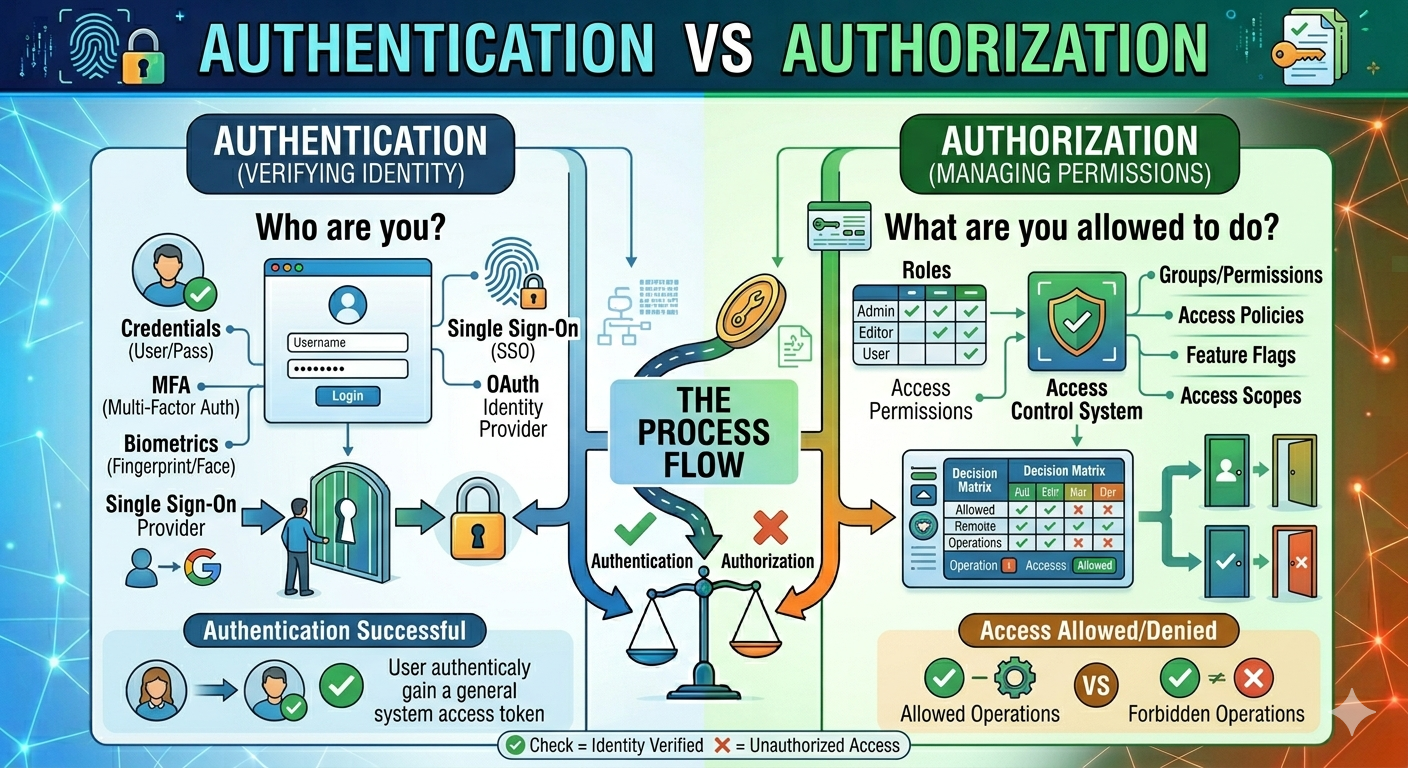
In modern web and application security, two terms are often confused: authentication and authorization. While they are closely related and often used together, they serve different purposes in terms of system and data security.
Understanding the difference between authentication and authorization is critical for developers, system administrators, and anybody else working with secure systems. In this post, we'll explain what each term means, how they work, and their key differences using real-world examples.
What Is Authentication?
Authentication is the process of validating a user's identity. It verifies that the person trying to access a system is who they claim to be.
Users can authenticate by providing credentials like username and password or email and OTP, or fingerprint/Face ID. The system verifies these credentials against stored data for successful authentication.
Common Authentication Methods
Password-based authentication
Two-Factor Authentication (2FA)
Biometric authentication (fingerprint, face recognition)
OAuth and social login (Google, Facebook)
For an example when you access your email account by entering your username and password, the system checks and confirms your identity. This verification process is referred to as authentication.
What Is Authorization?
Authorization is the process of determining what a user can do after being authorized. It specifies the rights and access levels within a system. It means once a user successfully authenticates, the system conducts a verification process to determine the resources available to the user and the actions.
Common Authorization Methods
Role-Based Access Control (RBAC)
Attribute-Based Access Control (ABAC)
Access Control Lists (ACL)
For an example the admin dashboard allows administrators to create, edit, and delete data, while normal users are restricted to viewing data. This access control mechanism is referred to as authorization.
How Authentication and Authorization Work Together
Authentication and authorization are closely connected and usually work together in a system:
User logs in (Authentication)
System verifies identity
System assigns role/permissions
User accesses allowed resources (Authorization)
In a banking application, after entering their username and password for authentication, users are granted access to view their account balance and make money transactions while being restricted from accessing other users' accounts. This access control is enforced using a several steps permission process. First, the user initiates the login process, which activates the authentication mechanism and confirms their identity. Once validated, the system assigns precise roles and permissions based on the user's identification, eventually providing access only to resources that they are authorized to use, ensuring security and compliance with access control policies.
Authentication vs Authorization – Key Differences
Authentication | Authorization |
|---|---|
Authentication verifies the identity of a user, ensuring they are who they claim to be before accessing the system. | Authorization determines the permissions of a user, deciding what actions or resources they are allowed to access after login. |
It answers, “Who are you?” by validating user credentials | It answers, “What can you do?” by checking roles and access levels. |
Authentication is always performed first, as the system must verify identity before providing access. | Authorization occurs after authentication, when the user's identity is confirmed. |
Uses credentials such as username, password, OTP, or biometrics to verify identity. | Uses roles, permissions, and policies to control access to resources. |
Identity verification is the main focus to ensure secure access. | Access control is used to restrict or allow specific actions. |
Authentication and authorization are critical elements of application security. Authentication confirms identification, whereas authorization manages access. Both collaborate to guarantee that only the right users have access to the the right resources.
Understanding these concepts is critical when developing safe, scalable, and reliable applications.