Network Security Basics – Threats & Protection Methods
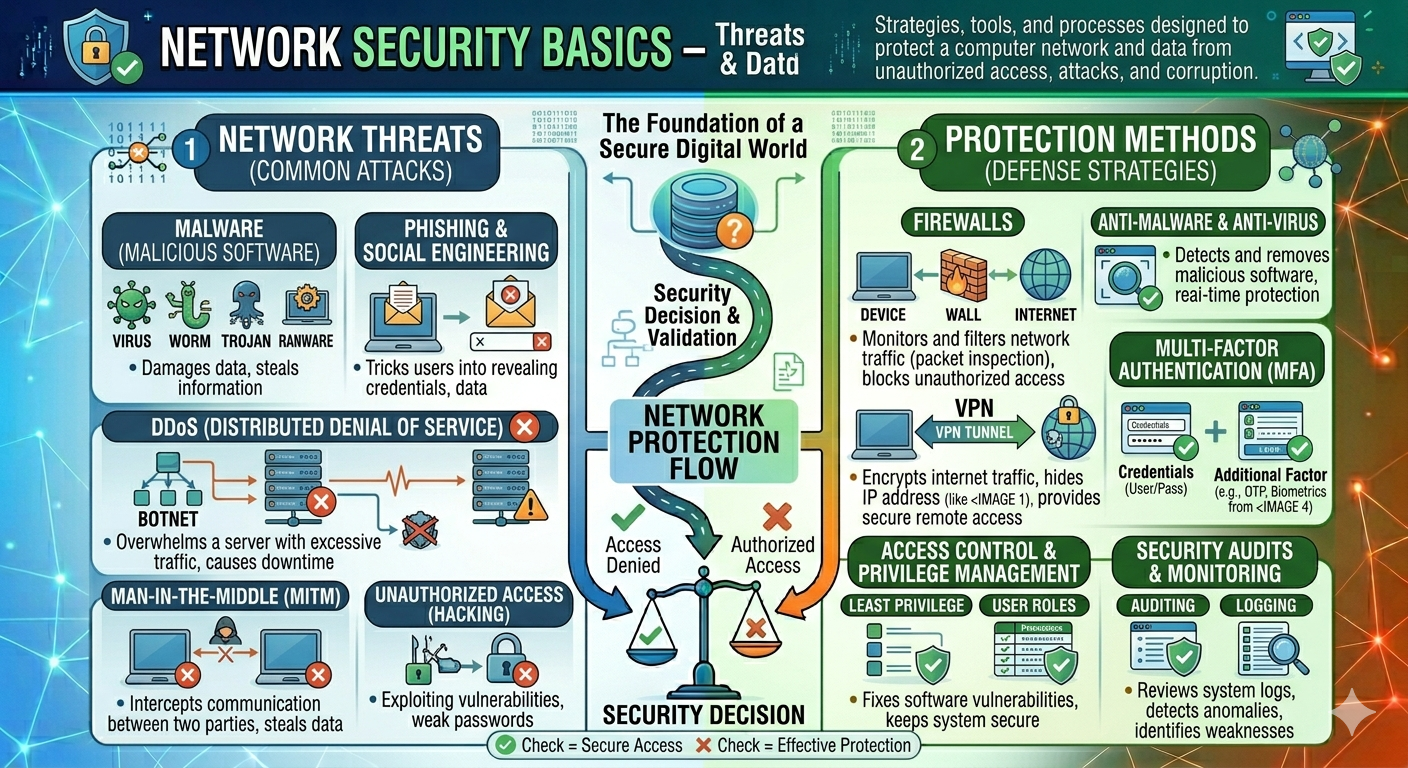
In today's interconnected world, computer networks serve as the foundation for businesses, governments, schools, hospitals, and personal communications. Every time we use the internet, access cloud apps, transfer money, or connect devices via Wi-Fi, data travels across networks. Network security aims to protect that data and the systems that process it.
Network security refers to the policies, methods, and practices used to protect computer networks against unauthorized access, cyberattacks, data theft, malware, and service disruptions. Effective network security maintains the confidentiality, integrity, and availability of information, referred to as the CIA Triad, a key concept in cybersecurity.
What Is Network Security?
Network Security is the process of protecting network infrastructure, connected devices, and transmitted data from unauthorized access, cyberattacks, misuse, modification, and destruction. It includes the policies, technologies, and procedures used to keep networks safe and ensure that only authorized users and systems can access sensitive information.
Data continuously flows across organizations across various platforms, making it vulnerable to attacks that can steal confidential information, modify important records, or disrupt services. Network security helps protects against these risks by monitoring traffic, restricting access, identifying suspicious behavior, and preventing malicious connections.
The main goals of network security
The primary objectives of network security are commonly described using in the CIA Triad, which refers to Confidentiality, Integrity, and Availability.
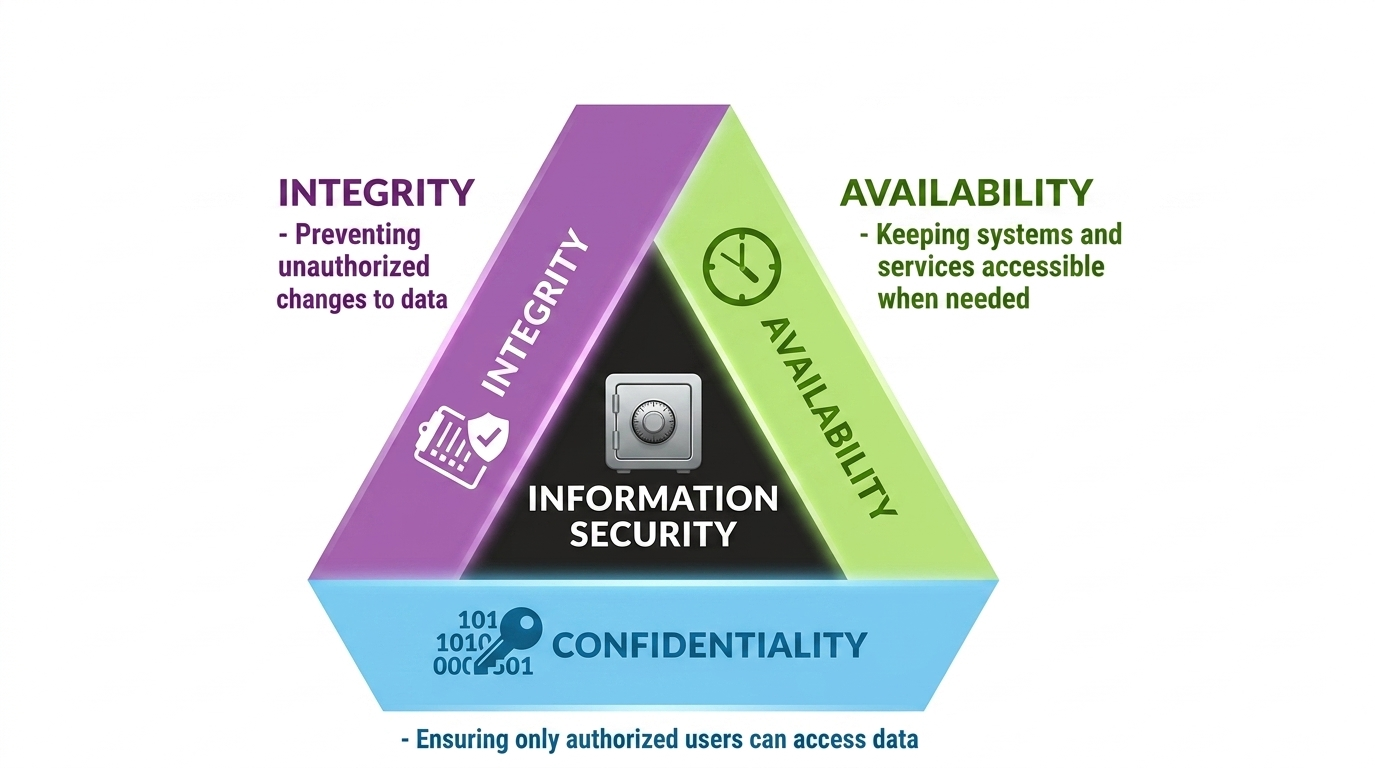
Confidentiality
Confidentiality ensures that sensitive information is only accessible to authorized users and systems. Passwords, financial records, medical information, and company documents should all be protected from unauthorized access.
For example, online banking websites use encryption and authentication to ensure that only the account owner has access to account information and transactions.
Integrity
Integrity ensures that data is valid and unaltered unless modified by authorized users. It protects data against unauthorized alteration, corruption, or tampering during in storage or transmission.
When a consumer makes an online payment, the transaction amount and recipient information must be exactly as submitted and not altered by attackers.
Availability
Availability ensures that systems, applications, and data are available when authorized users need them. Security measures should protect against downtime caused by cyberattacks, hardware failures, or misconfigurations.
For example, an e-commerce website should be available to consumers even amid high traffic or attempted denial-of-service assaults.
Imagine for a company office, locking sensitive documents in a secure cabinet represents confidentiality, ensuring no one can alter those documents without permission represents integrity, and allowing authorized employees to access the documents whenever they need them is referred to as availability as well. This way, network security applies these same principles to digital systems and data.
Network Security Threats
Computer networks face many security threats that can compromise data, disrupt services, and cause financial or reputational damage. Understanding these threats is the first step in implementing effective security controls. The following are some of the most typical network security threats that organizations and individuals encounter.
Malware
Malware is harmful software that is intended to harm systems, steal data, or gain unauthorized access. It includes viruses, worms, Trojans, ransomware, and spyware. For example, ransomware might encrypt company files and demand payment to restore access.
Phishing
Phishing is a social engineering attack in which attackers send out fake emails, messages, or websites that look to be authentic. Their purpose is to deceive users into revealing passwords, banking details, or other sensitive data.
Most of the time, hackers send out fake emails that appear to be from reliable sources like banking institutions, eBay, PayPal, and even colleagues and friends. Hackers use phishing attacks to trick users into performing a recommended action, such as clicking on links in emails that direct them to phony websites that ask personal information or download malware onto their devices. Opening email attachments can potentially lead to the installation of malware on users' computers that is intended to gather private data, send emails to contacts, or grant remote access to their machines.
Ransomware
Ransomware, on the other hand, is a type of virus in which cybercriminals use a malicious program or phishing emails to lock your device and then demand money to unlock it. It can even stop you from using your device at all. It might stop you from utilizing applications, encrypting your files, and so on.
DDoS (Distributed Denial-of-Service)
A form of DoS attack known as Distributed Denial of Service (DDoS) occurs when several trojan-infected systems target a single system and result in a DoS attack. To flood the targeted resource, a DDoS assault makes use of numerous servers and Internet connections. One of the strongest tools on the cyber platform is a DDoS attack. A DDoS attack has most likely been the cause of a website being pulled down when you learn about it. This indicates that hackers have attacked your website or computer by overwhelming them with traffic. This causes overloading, which crashes the machine or website.
Drive-by download attacks
Malicious code is downloaded from a website using a browser, app, or integrated operating system in a drive-by download attack without the user's knowledge or consent. The download is activated without the user having to click on anything. A download can begin just by opening a website or viewing it. Drive-by downloads are a common method used by cybercriminals to infect endpoints with exploit kits, other malware, and banking Trojans as well as to steal and acquire personal information.
Man in the Middle
When hackers interject themselves into a two-party transaction, a man-in-the-middle (MITM) assault takes place. Cisco claims that after halting the flow of transmission, they may filter and take information. When a visitor makes use of an unprotected public Wi-Fi network, MITM assaults frequently happen. Attackers place themselves in the way of the visitor and the network, then employ malware to set up malicious software and access data.
SQL Injection
A specific kind of cyberattack called a Structured Query Language (SQL) injection happens when malicious code is inserted into a server that supports SQL. The server divulges information when infected. Simply typing the malicious code into a search box on a susceptible website can submit it.
Spyware
Designing your device to collect data as soon as it's on your device, it can cause terrible problems. From stealing confidential financial information to permanently damaging equipment. They can easily watch you without your knowledge using a webcam or microphone. taking something of value from you. for instance, your passwords and other private information.
Exploit kits
A programming tool called an exploit kit lets someone without any prior experience writing software code to create, alter, and spread malware. A few other names for exploit kits are infection kits, crimeware kits, DIY attack kits, and malware toolkits. These toolkits are used by cybercriminals to distribute malware, perform denial-of-service attacks, create botnets, and steal corporate data by exploiting system weaknesses.
Unauthorized Access
Unauthorized access occurs when attackers gain entry to systems using stolen credentials, weak passwords, or unpatched vulnerabilities. Once inside, they may steal data or disrupt operations.
Insider Threats
Not all threats come from outside the organization. Employees, contractors, or partners may intentionally misuse access or accidentally expose sensitive information.
Packet Sniffing
Packet sniffing involves capturing network traffic to analyze transmitted data. If communications are not encrypted, attackers may obtain usernames, passwords, and other confidential information.
Protection Methods in Network Security
Organizations utilize a variety of security policies to protect their networks, systems, and data from cyber threats. Each protective approach addresses a specific type of risk, and together they form a layered defense strategy known as defense in depth. Instead, then relying on a single tool, firms mix multiple technologies and processes to reduce vulnerabilities and respond to attacks more effectively.
Firewall
A firewall is one of the most important network security tools. It analyzes incoming and outgoing network traffic and enables or denies connections based on established security policies.
For example, a company may set up a firewall to allow employees to access the web while blocking unauthorized attempts to connect directly to internal database servers. Firewalls can be implemented as hardware, software, or cloud-based services.
Antivirus and Anti-Malware Software
Antivirus and anti-malware software scans systems for viruses, ransomware, spyware, and trojans, and then restrictions and removes them.
These tools provide real-time security by monitoring files and processes, allowing infections to be detected before they cause system harm or steal important data.
Virtual Private Network (VPN)
A VPN establishes a secure, encrypted tunnel between a user's device and a private network via the internet. Remote employees commonly use VPNs to securely access internal company resources from home or while traveling. This helps to protect sensitive data from interception on public Wi-Fi networks.
Encryption
Encryption is the process of transforming readable data into an unreadable format known as ciphertext, allowing only authorized users with the necessary decryption key to access the original data. It protects both data in transit (information transferred over HTTPS-secured websites) and data at rest (information kept on encrypted hard drives and databases). As a result, even if attackers intercept encrypted data, they are unable to decrypt it without the appropriate key.
Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) enhances security by forcing users to verify their identities using two or more authentication factors. These criteria include something they know (like a password), something they have (such a mobile device or security token), and something they are (including biometric identifiers like fingerprints or facial recognition). Implementing MFA significantly enhances security, ensuring that even if a password is hacked, unauthorized access is prohibited by additional verification processes.
Access Control
Access control ensures that users only have access to the systems and data required for their roles. For example, a sales representative may be able to examine client information but not change payroll records. The concept of least privilege reduces the impact of compromised accounts and insider threats.
Regular Software Updates and Patching
Software vendors provide updates to fix security vulnerabilities and improve system stability. These patches promptly help prevent attackers from exploiting recognized weaknesses. Keeping operating systems, applications, and network devices up to date is one of the most effective security strategies.
Regular Backups
Backups are essential for creating copies of important data, allowing organizations to restore systems in case of ransomware attacks, accidental deletions, or hardware failures. Effective backup plans have several critical components, including automatic scheduling to ensure regular backups, secure storage to protect data from unauthorized access, and periodic testing of restoration procedures to ensure that data can be properly restored when needed.
Network Segmentation
Network segmentation divides a large network into smaller, isolated sections. For example, guest Wi-Fi can be separated from internal business systems. If one segment is compromised, the attack is less likely to spread throughout the entire organization.
Network security is a critical component of modern IT and cybersecurity. It protects networks, devices, and data against malware, phishing, unauthorized access, and denial-of-service attacks. Firewalls, encryption, VPNs, MFA, and other controls can help organizations reduce risk and maintain secure and reliable systems.
No single security tool can stop every threat. Strong network security uses multiple layers of protection working together. For example, a business may combine firewalls, encryption, MFA, antivirus software, and backups to create a comprehensive security strategy.